A global coalition of investigators has dismantled a sprawling botnet built on hacked home and small business routers, cutting off a criminal proxy service that quietly turned everyday internet connections into launchpads for fraud and cyberattacks. Authorities identified the network as SocksEscort, a pay-to-use proxy platform that monetized compromised devices to mask the true source of illegal activity, according to the Department of Justice.
Europol said the operation severed control over more than 369,000 routers and other Internet of Things devices across 163 countries, noting the service had been used to support ransomware operations, distributed denial-of-service campaigns, and the sharing of child sexual abuse material. The DOJ added that the scheme helped criminals plunder victims’ bank and cryptocurrency accounts and file fraudulent unemployment insurance claims, costing Americans millions. The service’s public website now displays a law enforcement seizure notice.
Unlike headline-grabbing malware that encrypts files or steals data outright, SocksEscort specialized in invisibility. Criminals bought licenses to channel their traffic through infected residential and small-office networks, inheriting the “clean” reputation of those IP addresses. The owners of those routers were typically unaware anything was wrong.
What investigators found about the SocksEscort botnet
Cybersecurity firm Black Lotus Labs, which worked with authorities on the takedown, said the botnet drew its power from malware known as AVRecon. The firm tracked roughly 280,000 infected routers as of last January and assessed that more than half of the victims were in the United States or the United Kingdom—prime ground for criminals aiming to blend into local internet traffic and defeat geo-based defenses.
Most targeted devices were small-office/home-office (SOHO) routers, which are often left running for years with outdated firmware, default passwords, exposed remote administration, or insecure services like UPnP. Once compromised, the routers quietly forwarded traffic for paying customers of the proxy service, making malicious connections look like they were coming from a neighbor’s living room rather than a known bad server.
How proxy botnets fuel crime and enable online fraud
Residential proxy botnets are prized because they grant access to IP addresses that fraud and abuse systems tend to trust. That advantage boosts success rates for credential stuffing and account takeovers at banks and crypto exchanges, helps crooks file benefits claims that appear to originate from the correct region, and lets ransomware affiliates scout targets and manage infrastructure without immediately tripping alarms.
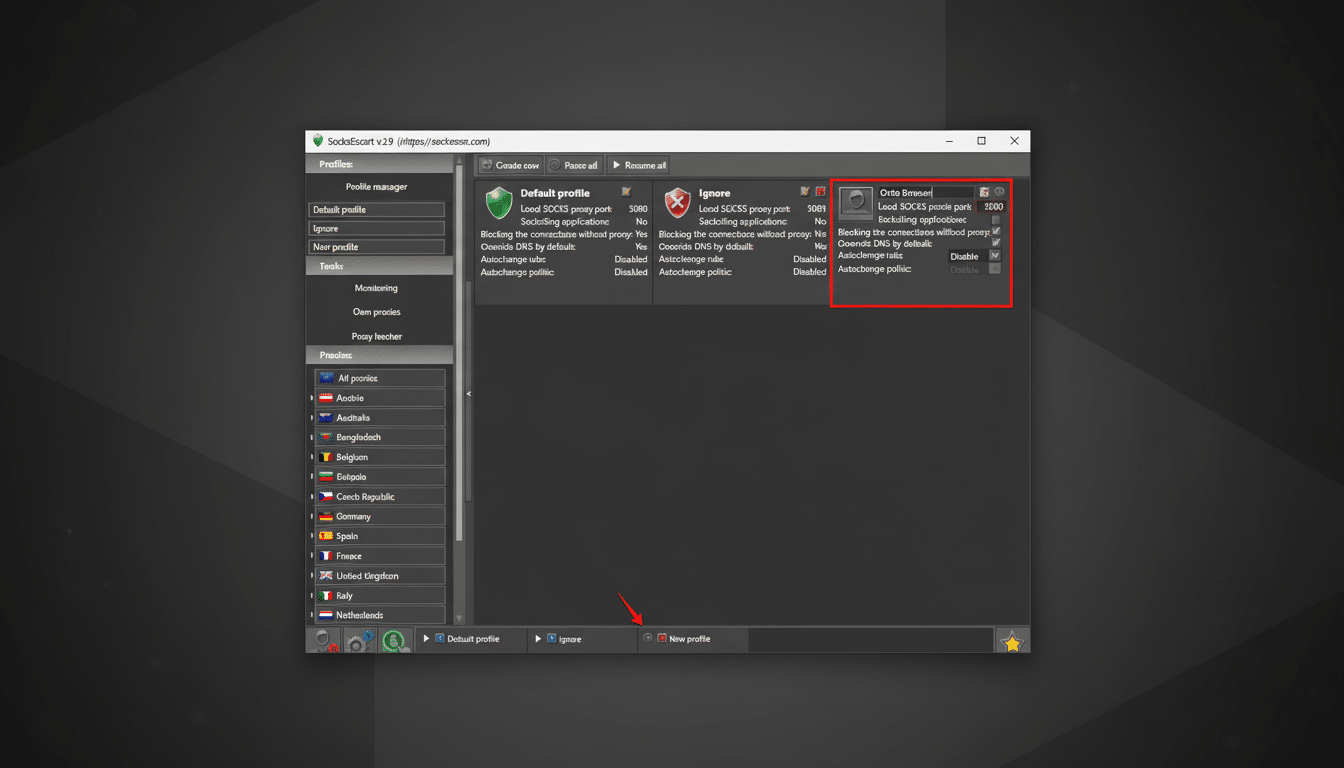
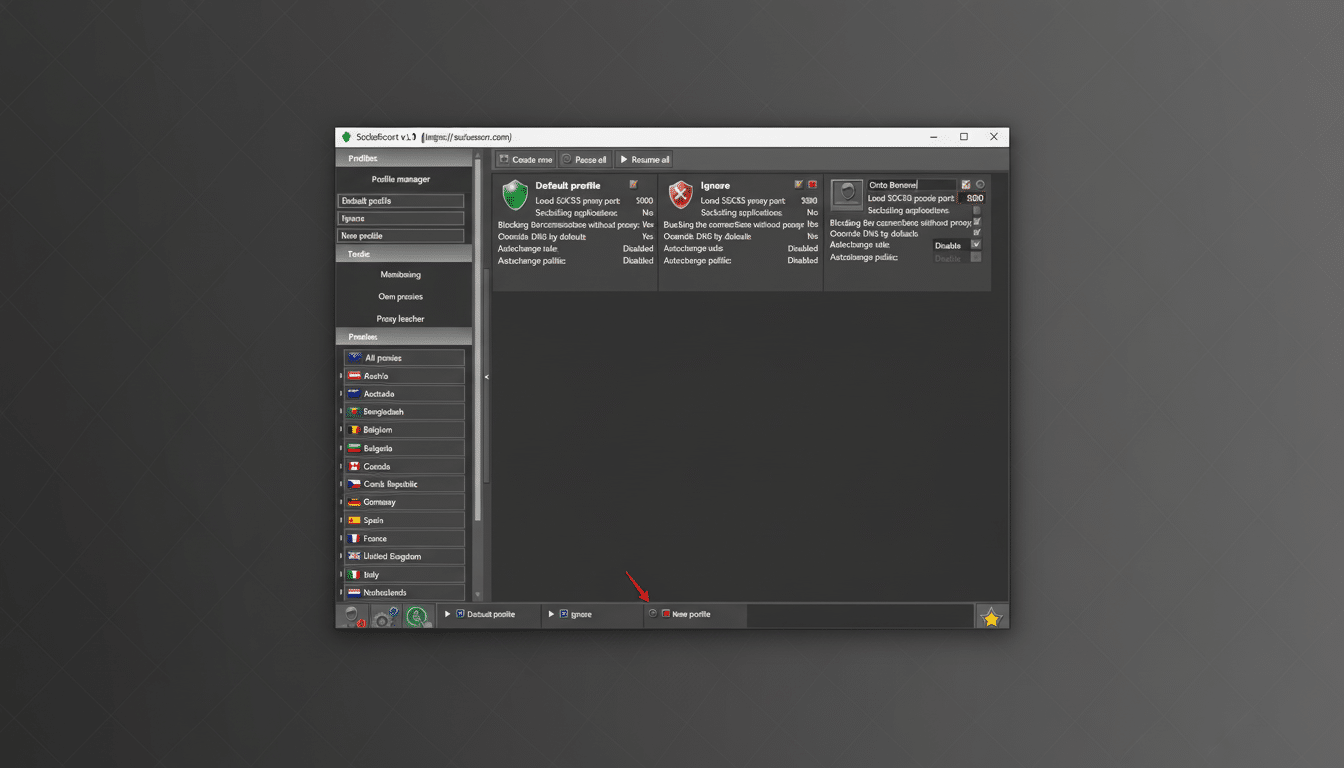
These services typically expose SOCKS or HTTP proxy endpoints to subscribers and rotate them frequently, complicating detection. The model feeds a broader cybercrime economy where stolen credentials, malware toolkits, and “infrastructure-as-a-service” are bought and sold at scale. For context, consumer fraud losses reported to the Federal Trade Commission surpassed $10B in 2023, underscoring how proxy-driven evasion can amplify the impact of scams and account abuse.
Takedown tactics and next steps after the disruption
Authorities used seizure warrants and coordinated infrastructure actions to neutralize SocksEscort’s control servers and payment flows, and to reroute or “sinkhole” connections from infected devices. Europol said compromised routers were disconnected from the service, diminishing criminals’ ability to exploit them at scale. That does not automatically disinfect the hardware, however; owners and ISPs still need to remediate devices to prevent re-compromise or reuse by copycat services.
Law enforcement agencies have grown more adept at combining legal pressure, infrastructure seizures, and private-sector telemetry to disrupt criminal platforms. This playbook mirrors recent operations that dismantled large-scale proxy and botnet services, aiming to impose real friction on criminals while pushing notifications to affected users through ISPs and vendors.
A long-running threat that targets SOHO routers
SocksEscort is not a new name in underground circles. Reporting by cybersecurity journalist Brian Krebs traced the service’s roots to 2009 as a Russian-language marketplace selling access to compromised systems. Black Lotus Labs later labeled SocksEscort “one of the largest botnets targeting SOHO routers in recent history,” reflecting a strategic shift from infected PCs to always-on edge devices that are harder for consumers to monitor.
The takedown also fits a pattern of actions against criminal proxy operations, including earlier efforts that targeted large-scale residential proxy networks. The common thread is recognizing that IP reputation laundering is a force multiplier for cybercrime—and that cutting off access to believable IP space is as important as seizing malware servers.
What router owners should do now to secure devices
Owners of home and small-business routers should update firmware from the vendor, change default administrator passwords, and disable remote administration from the internet unless absolutely necessary. If compromise is suspected, back up settings, perform a factory reset, then reapply updates before restoring only essential configurations. Review DNS settings for unauthorized changes and consider replacing end-of-life hardware that no longer receives security patches.
For organizations with remote or hybrid workforces, policies should cover router hygiene: require modern devices, enforce WPA3 or strong WPA2-Enterprise where possible, and provide guidance on disabling risky services like UPnP. ISPs and equipment makers can further reduce risk by enabling automatic updates, shipping with secure defaults, and offering clear remediation paths when threats like AVRecon surface.
This takedown is a meaningful blow to a bustling criminal utility. But as with past disruptions, the market will try to regenerate. Sustained pressure from coordinated law enforcement, paired with better-secured edge devices, is what will keep proxy botnets from quietly turning our routers into someone else’s crime tool.

