Google’s latest zero-day report delivers a stark message for corporate defenders: nearly half of all in-the-wild exploits the company tracked in 2025 hit enterprise technologies, with attackers zeroing in on the very appliances meant to safeguard networks. The finding underscores how the enterprise edge—firewalls, VPNs, and virtualization platforms—has become the fastest, most reliable path into high-value environments.
Enterprise Appliances Became Prime Targets
Google’s analysis attributes 48% of last year’s tracked zero-days to enterprise tech, and about half of those were in security and networking gear. Devices from Cisco and Fortinet, along with VPN and virtualization platforms from Ivanti and VMware, featured prominently. Each of these vendors has recently acknowledged real-world exploitation in customer environments, reinforcing that attackers are treating enterprise perimeter and infrastructure software as low-hanging fruit.
The common playbook wasn’t exotic. Researchers cited familiar classes of flaws—input validation errors and incomplete authorization checks—that enable remote code execution or authentication bypass. These bugs are straightforward to weaponize and, once exploited, can provide privileged access without tripping endpoint defenses that rarely run on hardened appliances.
Google also pointed to business application stacks as an underappreciated zero-day risk. A notable example was the Clop extortion gang’s campaign against Oracle E-Business Suite customers, which exposed sensitive HR records and executive data at organizations including Harvard University, American Airlines’ Envoy subsidiary, and The Washington Post. The takeaway: not all enterprise zero-days live at the edge—highly customized, mission-critical apps can be just as lucrative for data theft.
Consumer Zero-Days Climb With Mobile In Focus
The remaining 52% of zero-days were tied to consumer and end-user products from vendors like Microsoft, Apple, and Google. Operating systems dominated those cases, with mobile platforms seeing a noticeable uptick year over year. That aligns with broader threat intelligence from groups such as Google’s Threat Analysis Group and Citizen Lab, which have tracked sustained targeting of iOS and Android users through sophisticated exploit chains.
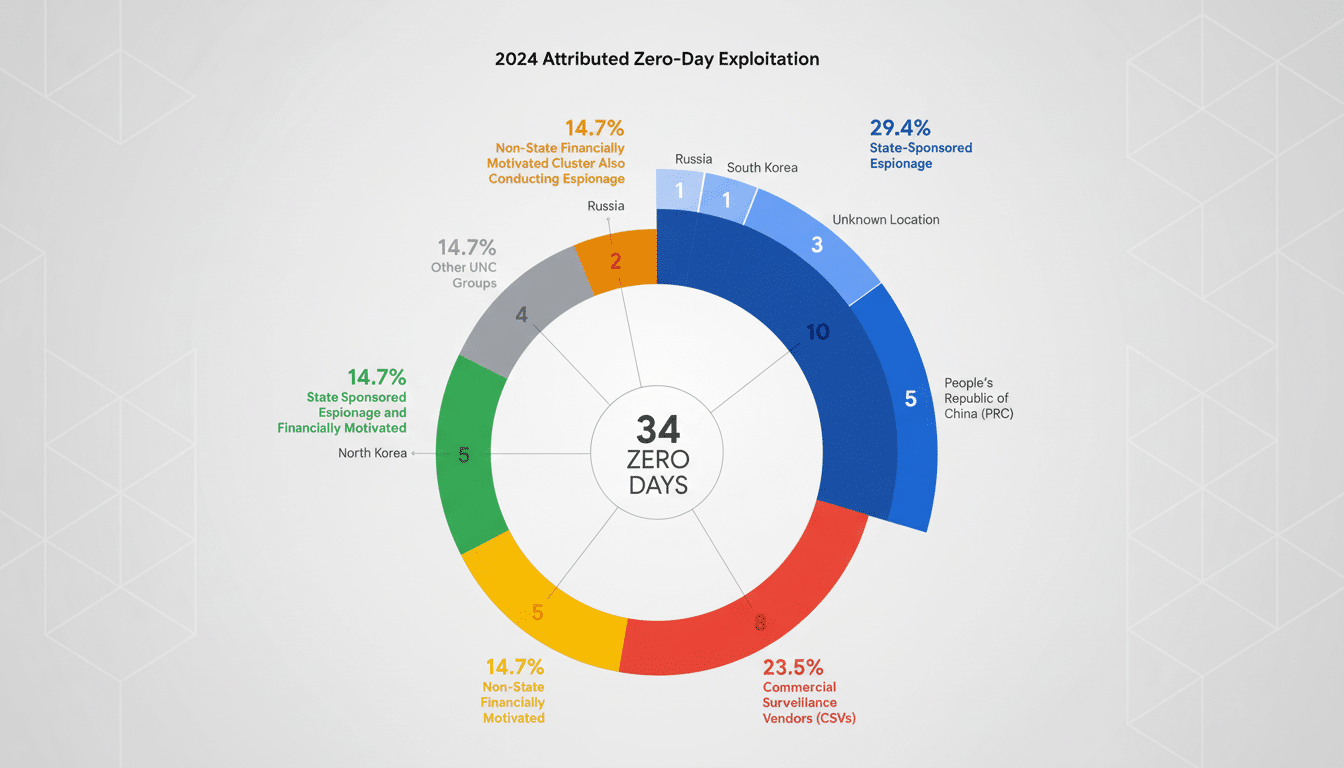
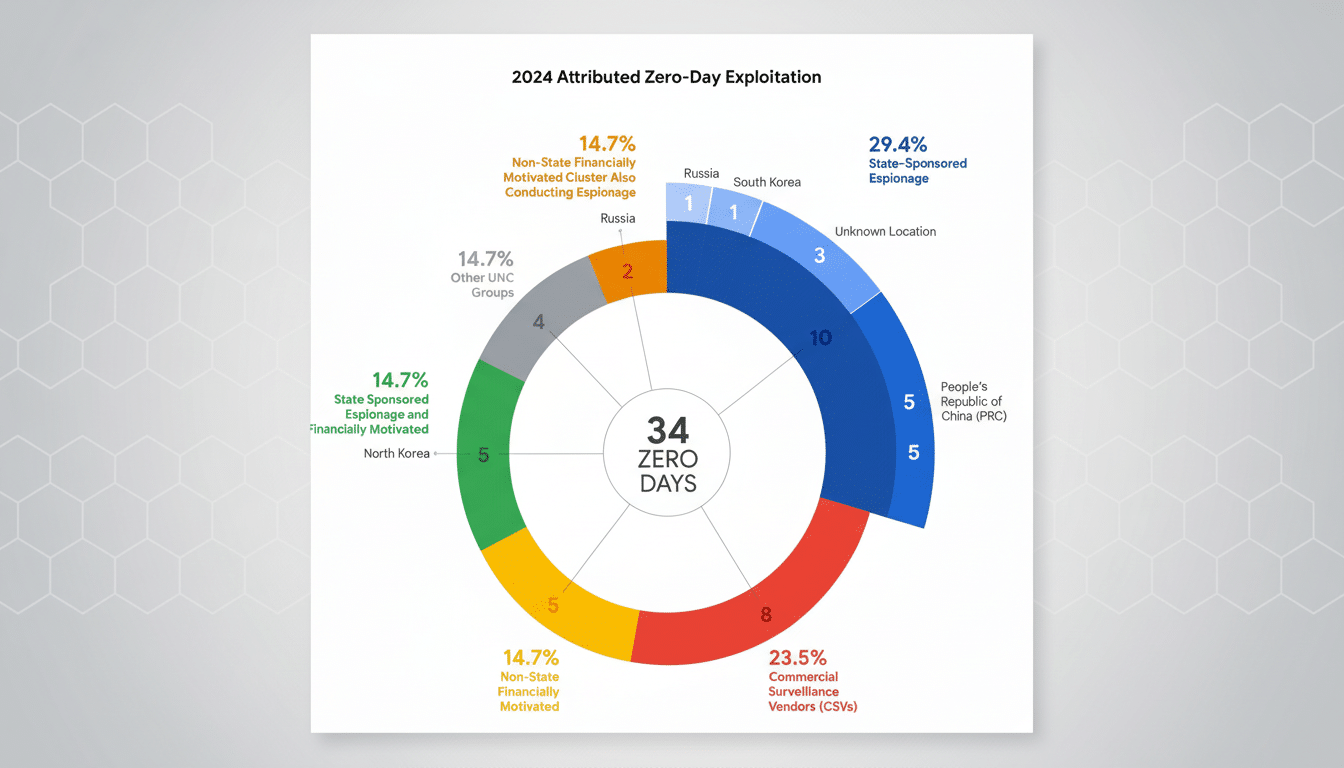
Google said more zero-days in 2025 were linked to commercial surveillance vendors than to traditional state-backed espionage units. This marks a slow but steady shift in the marketplace for intrusion capabilities, where governments increasingly procure turnkey exploits and spyware from private companies rather than building them entirely in-house. Firms previously named by independent researchers—including NSO Group and Intellexa—illustrate how this industry professionalizes access to advanced mobile exploits.
Why Perimeter Tech Keeps Getting Pwned So Often
Three structural realities explain attackers’ fixation on enterprise appliances. First, exposure: firewalls, VPN concentrators, SASE gateways, and hypervisor management interfaces are internet-facing by design, shrinking the distance between a bug and a breach. Second, visibility: most organizations lack robust telemetry on these devices, giving intruders a quieter foothold than a compromised laptop or server would. Third, patching friction: maintenance windows, clustering complexity, and fear of downtime slow updates, handing well-funded adversaries a larger exploitation window.
Those dynamics mirror patterns reflected by the CISA Known Exploited Vulnerabilities catalog, which has logged a steady drumbeat of edge-device flaws—think Citrix NetScaler, Cisco ASA, Fortinet FortiOS, Ivanti Connect Secure, and Atlassian Confluence—routinely leveraged in mass exploitation. Ransomware groups have likewise hammered virtualized environments; the wave of ESXi targeting in recent years showed how one hypervisor-layer compromise can cascade across dozens or hundreds of workloads.
What CISOs Should Do Now To Reduce Zero-Day Risk
Inventory and exposure control come first. Maintain a current map of all internet-facing appliances and management interfaces, and eliminate unnecessary public access via dedicated admin networks and strong access controls. Place device management planes behind SSO and MFA, and restrict by source IP whenever possible.
Harden patch operations. Treat perimeter and virtualization updates as emergency-change candidates with predefined rollback plans. Subscribe to vendor advisories and prioritize fixes for issues flagged by CISA’s KEV list or by reputable threat intel teams. Where immediate patching is impractical, deploy virtual patching via WAFs or reverse proxies to mitigate known exploit paths.
Improve detection on “black box” devices. Centralize logs from firewalls, VPNs, and hypervisors; enable any available debug or audit features; and baseline normal device behavior to surface anomalies like unexpected processes, config changes, or egress patterns. Network-based detection and honeypot listeners on management ports can provide early warning of exploitation attempts.
Finally, pressure vendors. Demand clear SLAs for security updates, public software bills of materials where feasible, and timely mitigations for zero-days. Favor products with rapid update channels, secure-by-default configurations, and support for memory-safe components in new code. As Google’s findings make clear, appliances can no longer be treated as set-and-forget guardrails—they are high-priority software assets that must be engineered, monitored, and patched with the same rigor as any business-critical application.

