Bumble is facing a proposed class action from a Texas user who alleges the dating app failed to safeguard highly sensitive personal information during a recent breach linked to the hacker collective ShinyHunters. The complaint argues the company did not employ reasonable security measures and left data exposed, putting millions of users at risk.
What the Lawsuit Claims About Bumble’s Data Security
The suit, filed in the Western District of Texas by plaintiff Tyra Omirin, contends that attackers infiltrated inadequately protected servers and accessed unencrypted personally identifiable information. According to the filing, the compromised data could include full names, birth dates, addresses, phone numbers, Social Security numbers, and account numbers.

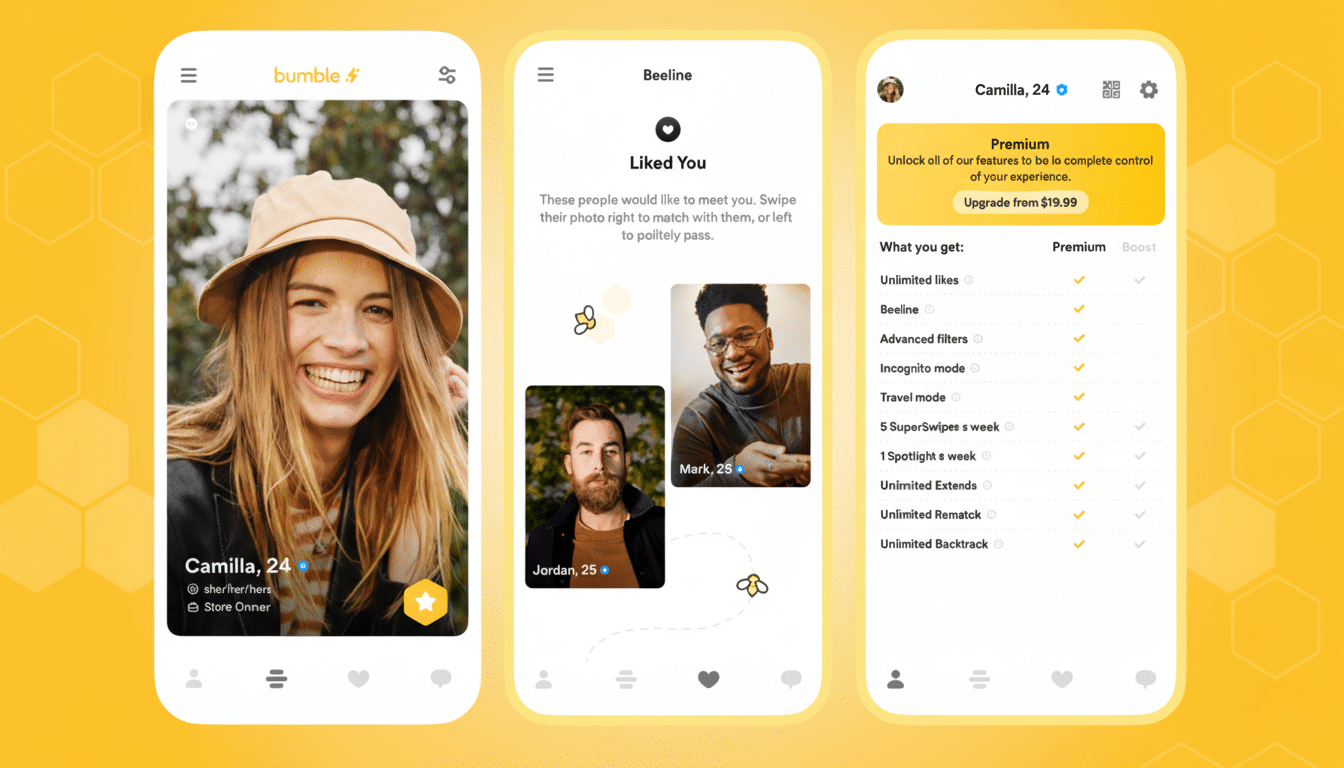
Omirin says she paid for Bumble’s services under the assumption the company would reasonably protect her information. She claims she would not have subscribed had she known otherwise and now spends time monitoring her accounts, exploring identity-theft protections, and managing the anxiety that comes with possible misuse of her data.
The complaint seeks damages and court-ordered security improvements, including:
- Encryption of all stored data
- Deletion of user information without a compelling retention need
- Independent third-party security audits
- Establishment of a formal information security program aligned with industry standards
Bumble’s Position And The Scope Of The Breach
ShinyHunters has claimed responsibility for obtaining roughly 30GB of Bumble-related data, according to reporting by Cybernews. A Bumble spokesperson told the outlet the company’s security team detected and cut off the intrusion, engaged outside experts, and notified law enforcement. The spokesperson said there was no access to the core member database, user accounts, the app itself, or direct messages and profiles.
Even when companies say the most sensitive stores were untouched, exposure of supporting systems can still be consequential. Metadata, partial identifiers, or logs can be combined to enable targeted phishing, account takeover, or identity fraud—a “mosaic effect” security researchers frequently warn about.
Who Are ShinyHunters, the Group Behind Recent Breaches
ShinyHunters is a well-known hacking group associated with large-scale data theft and rapid monetization of stolen databases on criminal marketplaces. In the same campaign, the group has also claimed intrusions at other major consumer brands, including a national bakery-café chain and entities tied to major dating platforms, according to threat-intelligence reports.
The group’s tactics typically exploit a mix of weak credentials, cloud misconfigurations, and vulnerabilities in third-party tools. The Verizon Data Breach Investigations Report has repeatedly found that the human element—phishing, credentials reuse, or misconfigurations—plays a role in the majority of breaches, accounting for roughly 68% of incidents.
Why This Case Matters For Dating Platforms
Dating apps aggregate particularly sensitive PII, as well as behavioral and location signals. That makes them attractive targets and places a premium on robust encryption, granular access controls, network segmentation, and continuous monitoring. Regulators in multiple jurisdictions have already scrutinized dating and social apps for data handling and adtech practices; a notable example was a European data protection authority imposing a multimillion-dollar penalty on a dating app for unlawful sharing of user information with advertisers.
The financial stakes are high. IBM’s Cost of a Data Breach report estimates the average breach now costs organizations about $4.88 million, with legal, remediation, downtime, and customer churn all contributing. Meanwhile, the Federal Trade Commission reports consumer fraud losses exceeding $10 billion in a recent year, and identity theft complaints remain above the million mark—evidence that exposed data often translates into real-world harm.
Beyond direct costs, class actions like this can drive binding security commitments. Courts have increasingly ordered companies to adopt baseline controls—encryption at rest, strong key management, role-based access, multifactor authentication, least-privilege policies, and independent audits—often drawing on guidance from NIST and CISA.
What Users Can Do Right Now to Protect Their Data
Users concerned about exposure can take immediate steps:
- Place a credit freeze with the major bureaus
- Enable alerts on bank and card accounts
- Use a password manager with unique credentials for every app
- Turn on multifactor authentication wherever possible
If you suspect misuse of your identity, federal resources such as IdentityTheft.gov offer personalized recovery plans. For companies, the takeaway is equally clear:
- Assume breach and deploy zero-trust principles
- Conduct regular tabletop exercises
- Require vendors to meet the same security bar
As the Bumble suit underscores, courts and consumers increasingly expect data protection to be built in—not bolted on after an incident.

