One successful cyberattack is enough to devastate a company—its reputation and its finances alike. Yet many organizations choose a provider for data center colocation based on price or availability, while secure colocation often ranks only third among their priorities. In the following lines, you will learn why data center security is the cornerstone of every decision and how to identify a provider that will truly protect your data.
Physical protection—the first line of defense in secure colocation
Many IT managers believe that once their servers are running somewhere in a rack behind locked doors, the job is done. Reality is different—according to the Uptime Institute study, 70% of incidents in data centers are caused by human factors, with unauthorized physical access accounting for a significant portion of these cases. Secure colocation begins in the parking lot, not at the server room door.

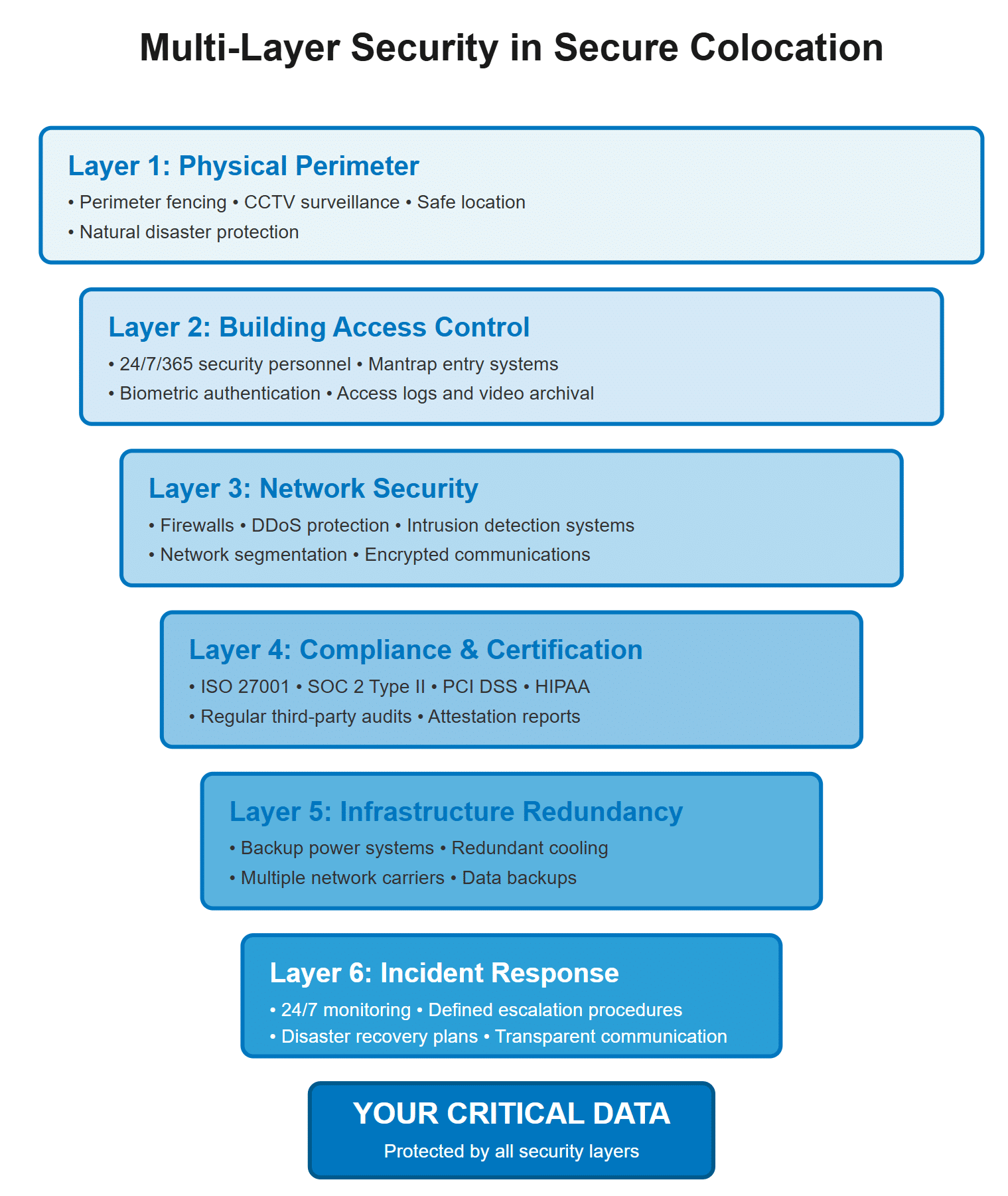
Top-tier data center security requires a multilayered approach to physical protection:
- perimeter fencing with a camera system as the first barrier,
- entry mantrap gates with biometric authentication,
- and on-site security personnel present 24/7/365.
Each additional layer increases the time and complexity of a potential intrusion, giving the security team the opportunity to detect and neutralize threats.
Detailed access logs play just as important a role as the physical security measures themselves. The provider should archive complete records, including video footage, for at least 90 days and allow you to review the access history to your equipment at any time. It is also essential to verify whether the facility is located outside flood zones and air traffic corridors—although these factors may seem minor, in the event of an incident they can determine the survival of your data.
Network security—the invisible shield around your data
Physical protection stops intruders at the door; network security protects your data from attacks that travel over the wire at the speed of light. Today, DDoS attacks exceed volumes of 1 Tbps and can take down even well-protected systems within minutes. Secure colocation must therefore include robust mechanisms for detecting and mitigating these threats.
Network segmentation is one of the most effective strategies for minimizing damage during an attack. Dividing infrastructure into isolated segments prevents attackers from moving freely across the network—even if they breach one barrier, they encounter another. Quality providers implement firewall-as-a-service solutions and intrusion detection systems (IDS) and apply security patches regularly before hackers can exploit vulnerabilities.
Encryption at both the network level and individual server level forms the final layer of protection for data in transit and at rest. Without it, every data transfer represents a potential security risk. Ask providers:
- which encryption protocols they use,
- how often they rotate keys,
- and whether they support end-to-end encryption for communication between your distributed systems.
Compliance certifications—the documents that save careers
Compliance certifications may seem like a bureaucratic formality at first—until an audit or legal dispute arises. That is when you realize that data center compliance certifications can mean the difference between a minor inconvenience and an existential corporate crisis. ISO 27001, SOC 2 Type II, or HIPAA are not just badges displayed on a website—they are proof that the provider has undergone an independent audit and met strict security standards.
When selecting a provider for data center colocation, request up-to-date audit reports, not just certification logos. Truly secure colocation means the provider regularly (typically annually) undergoes third-party assessments and documents the results with valid certifications. Also ask about certifications specific to your industry—financial institutions require PCI DSS, while healthcare organizations need HIPAA compliance.
An often-overlooked aspect of compliance is how the provider helps you meet your own regulatory obligations. A quality partner will supply the documentation necessary for your audits and, if needed, send a compliance specialist to participate in discussions with your auditors.
Incident Response—the plan B you hope you will never need
Perfect security does not exist—there are only varying lengths of time until the first breach. That is why secure colocation also depends on the speed and quality of response to a security incident. Providers without a clearly defined incident response plan are like firefighters without extinguishers—they look professional until the first fire breaks out.
An incident response plan must define escalation procedures, 24/7 contact points, and timeframes for each step. Ask:
- How quickly the provider informs you about suspicious activity.
- Who exactly will be your point of contact during the incident?
- What attack data they will provide for your own forensic analysis.
Also require regular disaster recovery tests—plans that have never been tested in practice usually fail when you need them most.
Transparency during a crisis is equally important. A provider that proactively informs you about every step of the resolution process enables you to make informed decisions and communicate effectively with your stakeholders. In contrast, a provider that remains silent during an incident and releases information in fragments deepens the crisis instead of resolving it.
Trust, but verify!
Security is not a box you tick during a single meeting—it requires a thorough audit and questions that many colocation providers would rather not answer. Start by:
- creating a list of security requirements specific to your company,
- scheduling a physical tour of the facility,
- and preparing a list of technical questions for the security managers.
Then evaluate the answers not only based on what is said, but also on how openly and thoroughly the information is shared.
Sources:
- https://ttc-teleport.cz/en/
- https://www.databank.com/resources/blogs/colocation-data-center-security/
- https://lightedge.com/6-considerations-secure-colocation-provider/

